SSL certificate monitoring is the continuous practice of tracking the health, validity, and configuration of SSL/TLS certificates across your web infrastructure. When a certificate expires, is misconfigured, or has a broken chain of trust, browsers display security warnings that drive away visitors — studies show 85% of users will abandon a site that shows a certificate error. The average organization experiences three certificate-related outages every two years, each costing approximately $2.86 million to resolve. Automated monitoring eliminates these entirely preventable failures.
Why SSL Certificate Monitoring Matters
The Shift to Shorter Certificate Lifespans
Starting in 2026, maximum certificate lifespans are shrinking from 398 days to 200 days, with a further reduction to 47 days planned by March 2029. This means organizations will need to renew certificates approximately eight times per year instead of annually. Manual tracking spreadsheets and calendar reminders cannot scale to this cadence — automated monitoring is now essential.
Browser Security Warnings Kill Traffic
When a certificate expires or fails validation, every major browser displays a full-page security warning. Users see "Your connection is not private" and most will close the tab immediately. This affects not only direct visitors but also search engine crawlers — Google will de-index pages it cannot access securely, directly harming your organic search rankings.
Compliance and Regulatory Requirements
Industries like finance, healthcare, and e-commerce operate under regulations (PCI DSS, HIPAA, SOC 2) that require encrypted data transmission. An expired or improperly configured certificate creates a compliance violation with potential fines and audit findings.
What to Monitor
Certificate Expiration Dates
The most critical metric. Set up tiered alerts at multiple intervals: 60 days for planning, 30 days for action required, 14 days for urgent, 7 days for critical, and 1 day for emergency. Different certificate types need different lead times — Extended Validation (EV) certificates require longer renewal processes than Domain Validation (DV) certificates.
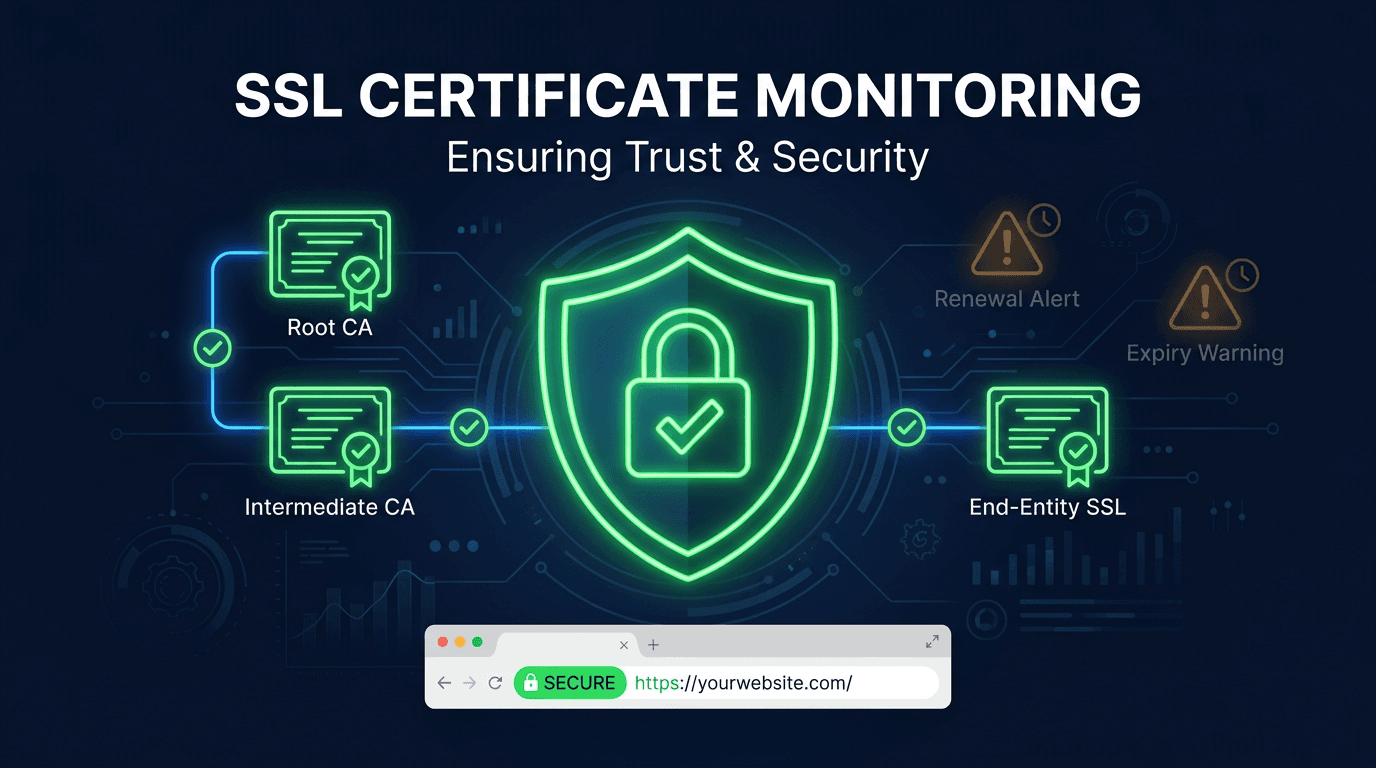
Certificate Chain Integrity
A valid leaf certificate is useless if the intermediate certificates are missing, expired, or in the wrong order. Chain validation tests the complete trust path from your server certificate through intermediates up to the trusted root CA. Broken chains are one of the most common causes of SSL errors, especially after certificate renewals or CA infrastructure changes.
Subject Alternative Names (SANs)
SANs define which domains a certificate covers. When a certificate is renewed, the new certificate might have a different SAN list — domains can be accidentally removed, breaking HTTPS for those subdomains. Monitor SAN coverage to ensure every domain and subdomain remains protected after renewals.
Protocol and Cipher Strength
Older TLS versions (TLS 1.0, 1.1) and weak cipher suites expose your site to known vulnerabilities. Monitoring should flag connections that negotiate deprecated protocols or ciphers, ensuring your encryption meets current security standards.
OCSP and Revocation Status
Online Certificate Status Protocol (OCSP) and Certificate Revocation Lists (CRL) tell browsers whether a certificate has been revoked. If your OCSP responder is slow or unreachable, browsers may delay page loads or show security warnings. Monitor OCSP stapling status and responder availability.
Best Practices for SSL Monitoring
Build a Complete Certificate Inventory
Document every domain with its certificate type, issuing CA, expiration date, auto-renewal status, and responsible team member. Many organizations are surprised to discover certificates on forgotten subdomains, staging environments, or legacy systems that nobody actively manages.
Monitor From Multiple Locations and Perspectives
A certificate might be valid from your office but expired on a specific CDN edge node. Test from multiple geographic regions, over both IPv4 and IPv6, and through different access paths (direct, through load balancers, through CDN). Each layer can serve a different certificate.
Automate Renewal With Verification
Automation (ACME/Let's Encrypt, cloud provider auto-renewal) handles the renewal itself, but monitoring must verify that automated renewal actually succeeded and that the new certificate was deployed to all endpoints. A renewal that completes but fails to deploy is just as bad as no renewal at all.
Monitor the Entire Infrastructure, Not Just Production
Staging, development, and internal tool certificates are commonly neglected. An expired certificate on an internal API can break CI/CD pipelines, monitoring systems, or employee-facing tools with no obvious external symptoms.
Track Certificate Transparency Logs
Certificate Transparency (CT) logs publicly record every certificate issued for your domains. Monitoring CT logs helps detect unauthorized certificate issuance — if someone obtains a certificate for your domain without your knowledge, CT monitoring alerts you to a potential compromise.
Common Mistakes to Avoid
Relying on Calendar Reminders
Calendar-based tracking fails because people change roles, ignore reminders, or lose track of which certificates belong to which systems. Automated monitoring tools provide reliable, up-to-date status regardless of team changes.
Only Monitoring the Leaf Certificate
The leaf certificate can be perfectly valid while an expired intermediate certificate breaks the trust chain. Always validate the complete chain, including intermediates and cross-signed certificates.
Ignoring Wildcard Certificate Scope
A wildcard certificate for *.example.com does not cover example.com itself or multi-level subdomains like api.v2.example.com. Verify that your wildcard coverage matches your actual domain structure.
Forgetting About Non-Web Services
SSL certificates protect more than websites. Email servers (SMTP, IMAP), VPN endpoints, API gateways, database connections, and IoT devices all use certificates that require monitoring.
Use Cases
E-Commerce Platforms
Payment processing requires uninterrupted HTTPS. Certificate failures during checkout directly cause abandoned carts and lost revenue. Multi-domain certificates covering storefronts, payment gateways, and API endpoints all require continuous monitoring.
SaaS and API Providers
API consumers depend on valid certificates for secure data exchange. An expired certificate breaks every client integration simultaneously, causing support ticket floods and potential SLA violations.
Financial Services and Healthcare
Regulatory compliance demands encrypted connections. Certificate monitoring provides the audit trail proving continuous compliance with PCI DSS, HIPAA, and SOC 2 encryption requirements.
Multi-Domain Organizations
Companies managing dozens or hundreds of domains need centralized certificate visibility. Monitoring aggregates certificate status across the entire portfolio, eliminating blind spots on forgotten or inherited domains.
How UpScanX Handles SSL Monitoring
UpScanX continuously monitors SSL certificates across all your domains, checking expiration dates, validating certificate chains, verifying SAN coverage, and testing protocol strength. The platform sends tiered alerts at 30, 14, 7, and 1 day before expiration through email, SMS, Slack, and webhooks.
Multi-perspective monitoring tests certificates from 15+ global locations, catching CDN edge issues and regional certificate mismatches. The dashboard provides a unified view of every certificate's status, issuer, expiration date, and chain health. Combined with uptime and domain monitoring, UpScanX ensures your HTTPS infrastructure remains secure, compliant, and trusted by every visitor.
SSL Certificate Monitoring Checklist
If you want a practical starting point, begin with five controls: maintain a complete certificate inventory, alert well before expiration, validate the full chain, confirm SAN coverage after every renewal, and test from multiple regions. Those five checks prevent the majority of certificate-related incidents teams see in production.
For more mature environments, add Certificate Transparency monitoring, OCSP stapling checks, policy-based issuer controls, and deployment verification across load balancers, CDNs, and staging environments. SSL monitoring works best when it is treated as an ongoing operational process, not a yearly renewal reminder.
That is especially true for teams managing many subdomains, multiple cloud providers, or frequent release cycles. The more distributed your edge infrastructure becomes, the more valuable continuous SSL visibility becomes.
Protect your certificates with UpScanX — start monitoring for free today.